These docs are for Cribl Edge 4.13 and are no longer actively maintained.
See the latest version (4.18).
Members
Control access to Cribl products by inviting and managing Members.
Members work together with Teams and Permissions to enable fine-grained access control and authorization.
Availability
Member- and Permission-based access control is available on:
- On-prem Distributed deployments (Stream, Edge) with certain plan/license tiers.
- All Cribl.Cloud deployments, at the Organization level. (Cribl.Cloud with certain plan/license tiers also offers granular access control on products, Fleets, and lower-level resources.)
On on-prem Single-instance deployments, or Distributed deployments with other licenses, all users will have full
Admin-level privileges.
Initial Permissions
When you first deploy Cribl Edge with the above prerequisites, you will be granted the Organization-level Admin Permission. Using this Permission, you can then assign additional Permissions to yourself and other Members.
Cross-Compatibility
Members and Permissions are available as the successors to Cribl’s original role-based access control (RBAC) model of Local Users and Roles/Policies. The earlier model is still supported across most of the Cribl product suite.
However, Cribl.Cloud invitations and Stream Projects have fully transitioned to the new model. For detailed differences between the two access control systems, see Which Access Method Should I Use?.
Known Issue
Existing Local Users display in Settings > Global > Members and Teams with the
No AccessPermission even if they’ve been assigned a higher Role. This is a display-only bug: These users’ original Roles still function as configured. For details and fix progress, please see Known Issues.
Organizations
The Members and Permissions model uses the concept of Organization as a container for the deployment of a whole suite of Cribl products (Stream, Edge, and Cloud-only Search and Lake).
In Cribl.Cloud, each account has one Organization. Use Workspaces for multi-tenancy within your Organization. Contact Cribl Support if you have a use case that requires more than one Organization.
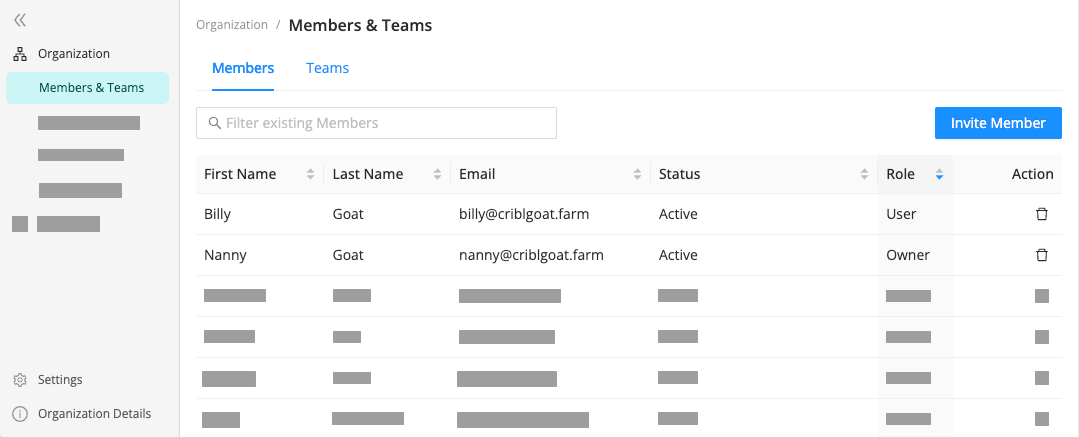
To access the Organization-level Members as an Admin:
- On the top bar, select Products, and then select Cribl.
- In the sidebar, select Organization, and then select Members & Teams.
- Here, you can select an existing Member’s row to change their access Permissions or other details, or select Invite Member to grant a new user access to your Cribl Organization.
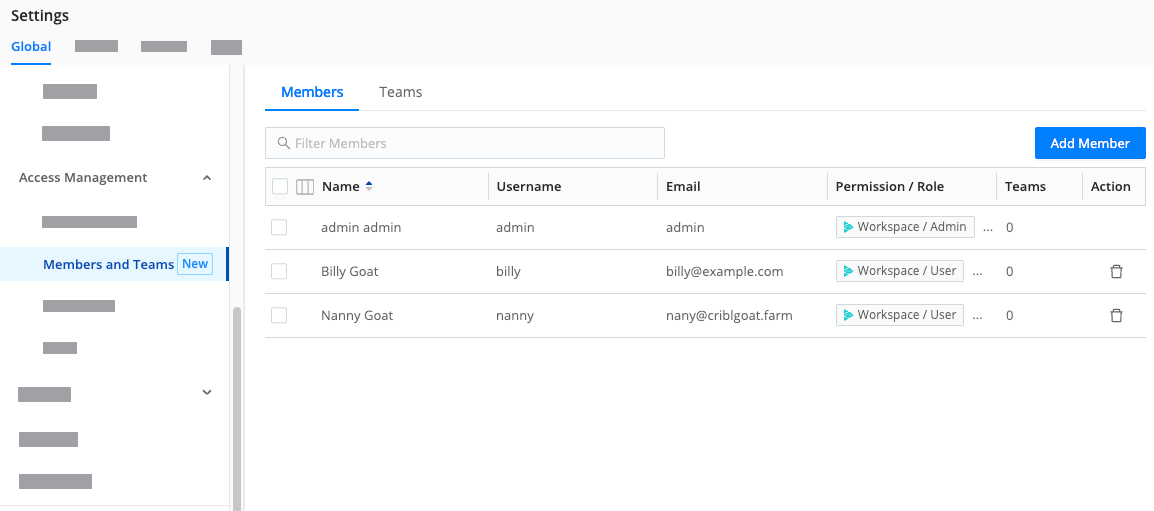
- In the sidebar, select Settings, then Global.
- Under Access Management, select Members and Teams.
- Here, you can select an existing Member’s row to change their access Permissions or other details, or select Add Member to grant a new user access to your Cribl Organization.
Invite Members
To invite new Members to your Organization:
- On the top bar, select Products, and then select Cribl.
- In the sidebar, select Organization, and then select Members & Teams.
- On the Members & Teams submenu, select Members.
- Select Invite Member.
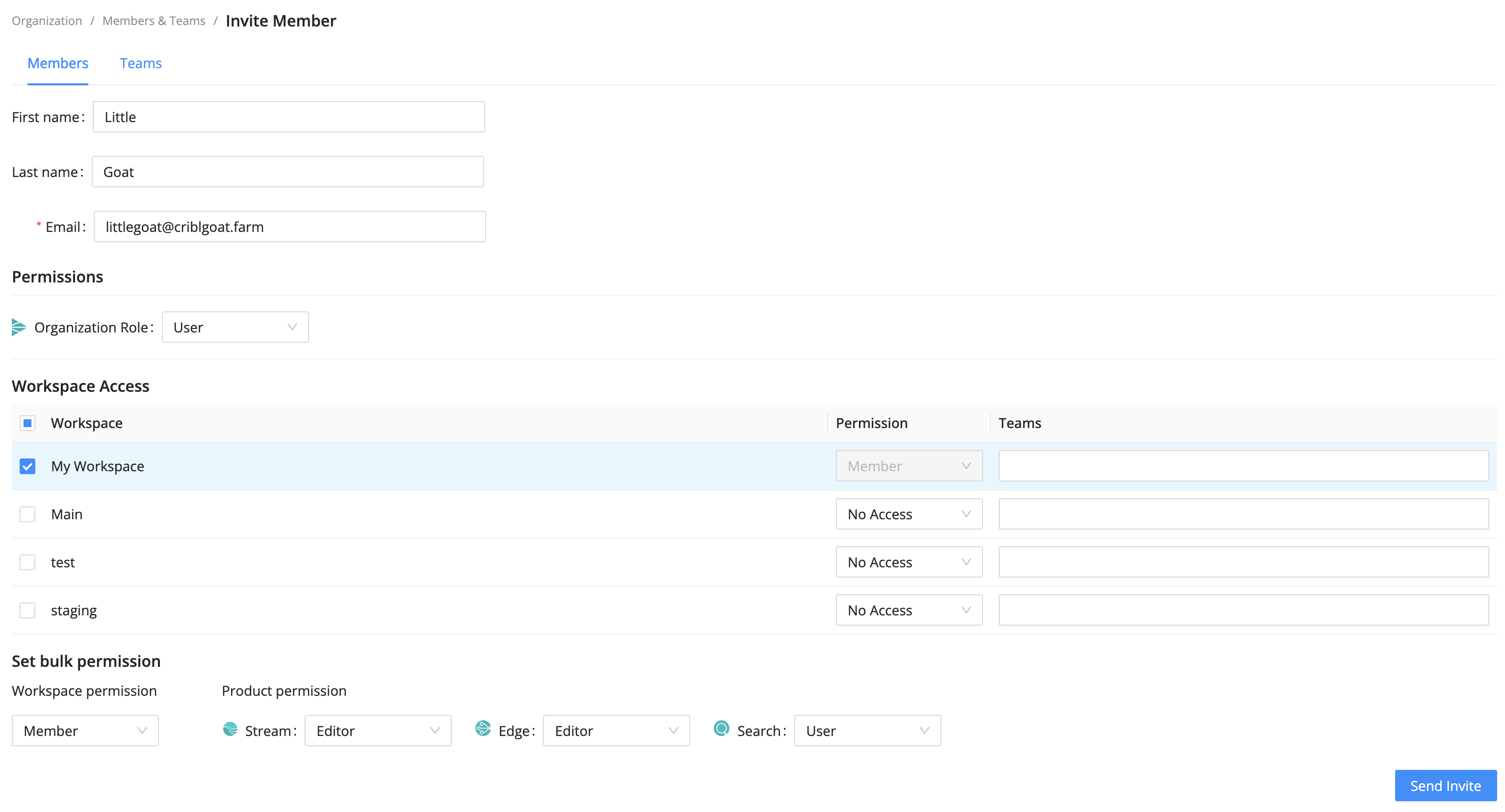
Enter the Email of the new user you want to invite.
Optionally, enter the First name and Last name for the user.
Under Permissions, assign an appropriate Organization-level Permission for the Member.
If you selected the User role, under Workspace Access, define access to specific Workspaces.
Assigning the User role requires an Enterprise plan. For details, see Pricing.
If you selected the Member Permission for any Workspace, additionally select product-level Permissions for that Workspace.
Select Send Invite to send the invitation.
- In the sidebar, select Settings, and then select Global.
- Under Access Management submenu, select Members and Teams.
- Select Add Member.
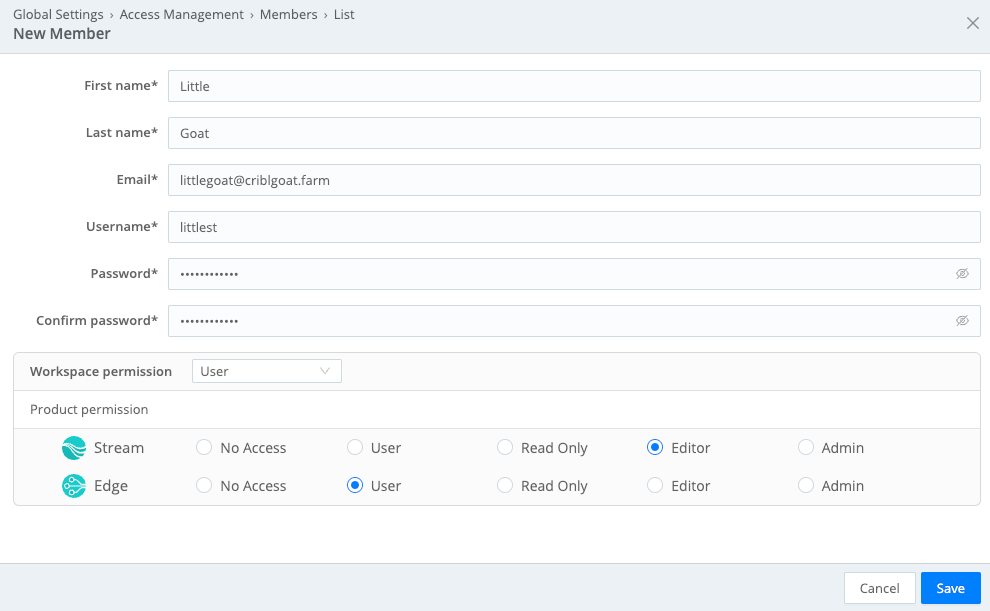
- Enter the new Member’s information, email, and password.
- Under Workspace permission, select the permission you want to grant to the new Member for the whole Organization.
- If you chose the User permission, configure access for each Cribl product separately. An Admin permission automatically grants admin access to all products.
- When finished, select Save.
Responding to Invites
When you send an invite from a Cribl.Cloud deployment, the new Member receives an email with an Accept Invitation link to either sign into their existing Cribl.Cloud account, or sign up to create an account and its credentials.
After a Member signs in, they’ll have access to your Organization and Cribl Edge instance at the Permission level you’ve specified.
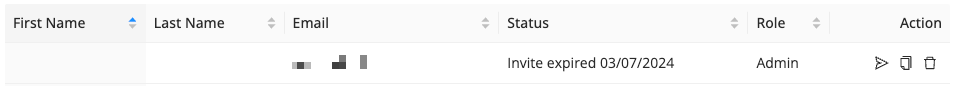
Manage Cribl.Cloud Invites
While an invite is pending, the Members & Teams page offers you these options in the Action column to deal with commonly encountered issues:
- Resend Invite: If your invited Member didn’t receive your invitation email, you can select this button to resend it.
- Copy Invite Link: If emails aren’t getting through at all, select this button to copy and share a URL that will take the invitee directly to the signup page. This target page encapsulates the same identity, Organization, and Permission you specified in the original email invite.
- Revoke Invite: This is for scenarios where you need to revoke a pending invite. (You sent someone a duplicate invite, your invitee is spending too much time in space to be a productive collaborator, etc.) After selecting this button, you’ll see a confirmation dialog.
An invite expires after seven days if it has been neither accepted nor revoked. It must then be resent.
Remove Members
To remove a Member from your Organization:
- In the sidebar, select Organization, and then select Members & Teams.
- Select Members, and next to the Member you want to remove, select Remove Member from the Action column.
Users will retain access to any other Cribl.Cloud Organizations they own or are Members of.
- In the sidebar, select Settings, and then select Global.
- Under Access Management submenu, select Members and Teams.
- Select Members, and next to the Member you want to remove, select from the Action column.
Removing SSO Members
If your Cribl.Cloud Organization is using SSO integration, the IDP (identity provider) admin manages Members in the IDP system. When you remove such a Member from the IDP, they will still be left in the Members list in the UI.
After removing the Member from the IDP, you also need to manually delete them from the Members list in the Cribl.Cloud Portal to completely remove them from the UI.
Members and Local Users
In on-prem deployments, Members and Local Users are interchangeable: Members can be reconfigured using legacy Roles instead of Permissions, and anyone you add to Local Users will also show in Members.





